One Billion Android Smartphones Vulnerable to Eavesdropping
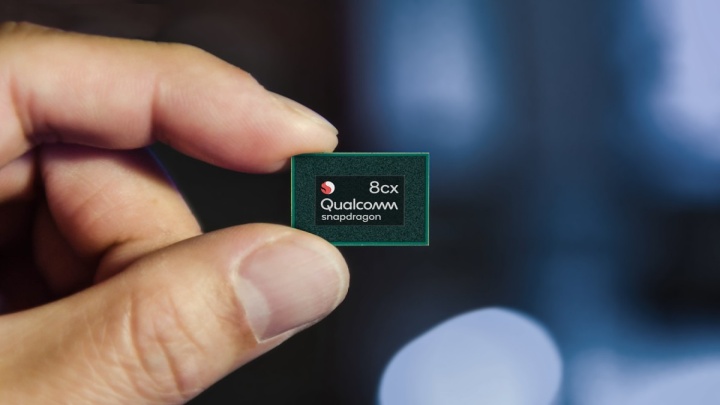
A large vulnerability in Qualcomm's component security systems has been discovered. The consequence of the security hole could expose many Android smartphones to eavesdropping.

- Check Point Reasearch has discovered a vulnerability in security measures of Qualcomm's chips;
- The problem may affect up to one billion devices worldwide;
- The vulnerability can be exploited to e.g. listen to conversations on a hacked phone.
Cybersecurity company Check Point Research discovered a vulnerability in Qualcomm components. As it turns out, the scale of the problem is huge, because Qualcomm's components are used in 1/3 of the world's smartphones, or roughly one billion Android devices. The gamp in the security systems can be used by hackers, among other parties, to get our SMS and call history, and even eavesdrop on our voice conversations or unlock the SIM card. The problem may affect all Android smartphones that have a chip model vulnerable to attack, including devices from Samsung, LG, Xiaomi, OnePlus, as well as Pixel from Google, especially when it comes to flagship models.
The source of the problem is the MSM (Mobile Station Modem) chip responsible for managing the device and wireless networks like 4G, 5G or LTE. Hackers may use QMI (Qualcomm MSM Interface) protocol that allows for communication between different MSM components. The QMI voice service can be used by attackers to inject malicious code into QuRT (Qualcomm's real-time OS), and take control of the aforementioned functions of our smartphone. The vulnerability can be a threat to up to 30% of all smartphones in the world.
Fortunately, Qualcomm is aware of the scale of the problem - already in December 2020 the company conducted the first patching of security systems. Unfortunately, it was not specified which smartphone models were included in this process. More information about the vulnerability is expected to be given in the June Android Security Bulletin, number CVE-2020-11292. It is not yet known when the next security patches will be introduced, but it is likely that flagships will be "patched" first, while lower and mid-range devices will have to wait longer.
- iPhone Air will be Apple's first smartphone in 10 years without stereo sound. Fans are not bothered by this
- A critical security flaw in Unity Engine was discovered after 8 years. It puts players at risk, and now all games need an urgent patch
- “This was not a breach of Discord,” the company clarified, dismissing rumors. Still, reports say that over 2 million “items” were stolen from a third-party vendor
0

Author: Michal Ciezadlik
Joined GRYOnline.pl in December 2020 and has remained loyal to the Newsroom ever since, although he also collaborated with Friendly Fire, where he covered TikTok. A semi-professional musician, whose interest began already in childhood. He is studying journalism and took his first steps in radio, but didn't stay there for long. Prefers multiplayer; he has spent over 1100 hours in CS:GO and probably twice as much in League of Legends. Nevertheless, won't decline a good, single-player game either.
Latest News
- Original War: Sand of Siberia with six new maps and improved new campaign
- gamescom latam 2026 brings new games that Your Wishlist is definitely missing
- To celebrate the 25th anniversary of Return to Castle Wolfenstein, the game will receive levels that were previously available only on consoles. All thanks to the fans
- Ashes: Blackwater is a free post-apocalyptic first-person shooter and a spin-off to one of the best best games made on Doom II engine
- A fan-made remaster of Heroes of Might and Magic 2 now with new maps. Fheroes2 has received a major update

