KNOB - Serious Security Gap Detected in Bluetooth
Bluetooth SIG Engineers recently published a note concerning a serious bug in the specification of the Bluetooth standard. It describes an exploit called KNOB that enables attacks on almost any Bluetooth Classic-compatible device and data interception.

A group of engineers discovered a critical bug in the Bluetooth specification that makes millions of devices around the world vulnerable to data theft. The Bluetooth SIG organization, which reviews the standards of the technology, has published a safety note in which it informs of the KNOB method.
The problem lies with Bluetooth itself
The way to bypass the security features is clever and consists in forcing the length of the cryptographic key to change to only 8 bits (the Bluetooth standard allows the use of keys with a length of 8 to 128 bits), which is very easy to crack (its only 256 combinations to check). This ensures that intrusion is not too difficult, and the connection allows you to capture data transferred between devices, such as audio or data.
Worse still, using this exploit allows the attacker to also connect to already paired devices. As it turns out, however, the problem only applies to devices with a BR/EDR Bluetooth compatible module (also known as Bluetooth Classic) or with dual-mode capability. Devices using the Bluetooth LE version, i.e. the alternative, low-energy standard, are not vulnerable.
Bluetooth - naked and defenseless...
An attack attempt can only be effective if both sides of the connection are susceptible to the KNOB method. At this point in time, however, it seems that the problem applies to most Bluetooth Classic devices from version 1.0 to 5.1.
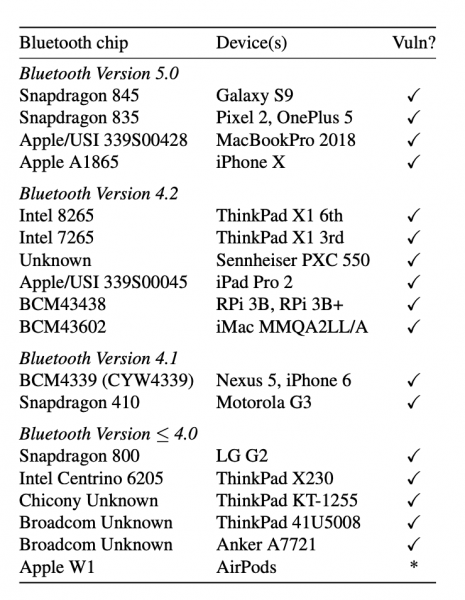
"The KNOB attack is possible due to flaws in the Bluetooth specification. As such, any standard-compliant Bluetooth device can be expected to be vulnerable. We conducted KNOB attacks on more than 17 unique Bluetooth chips (by attacking 24 different devices). At the time of writing, we were able to test chips from Broadcom, Qualcomm, Apple, Intel, and Chicony manufacturers. All devices that we tested were vulnerable to the KNOB attack," said the discoverer of the gap.
Companies such as Apple and Microsoft have already released patches, which are aimed at neutralizing the danger. The basic specification of the Bluetooth standard, which increases the minimum length of the cryptographic key to 56 bits, has also been changed. However, to combat this "serious threat to the security and privacy of Bluetooth users", as identified by its discoverers, it is necessary to update all devices as soon as the appropriate patches are available. This does not change the fact that it's yet another serious security breach that's been with us for a very long time.
- A critical security flaw in Unity Engine was discovered after 8 years. It puts players at risk, and now all games need an urgent patch
- Just 10 days until Windows 10 support ends. Here’s what you need to know
- “This was not a breach of Discord,” the company clarified, dismissing rumors. Still, reports say that over 2 million “items” were stolen from a third-party vendor
0
Latest News
- The Best James Bond PC video games and mods that improve them
- Return to Castle Wolfenstein on PC has recieved a fan DLC with singleplayer maps that were previously available only on consoles
- Original War: Sand of Siberia with six new maps and improved new campaign
- gamescom latam 2026 brings new games that Your Wishlist is definitely missing
- Ashes: Blackwater is a free post-apocalyptic first-person shooter and a spin-off to one of the best best games made on Doom II engine

